
WordPress Security Issues 2022
On the off chance that you own a WordPress-controlled site or are thinking about involving WordPress as your CMS, you might be worried about the potential 5 Common WordPress Security Issues 2022. Here, we’ll lay out a couple of the most widely recognized WordPress security weaknesses, alongside steps you can take to get and safeguard your WordPress site.
Is WordPress Secure?
The solution to the inquiry “is WordPress secure?” is it depends. WordPress itself is exceptionally secure the length of WordPress security best practices are followed.
As per the most recent use of content administration frameworks information from W3Techs, WordPress currently controls 43.3% of all sites. So WordPress security weaknesses are unavoidable in light of the fact that not all clients are cautious, exhaustive, or security cognizant with their sites. Assuming a programmer can observe away into one of the huge numbers of WordPress sites on the web, they can examine for different sites that are likewise running unreliable arrangements of old or shaky renditions of WordPress and hack those as well.
WordPress runs on open source code and has a group explicitly dedicated to finding, distinguishing, and fixing WordPress security gives that emerge in the center code. As security weaknesses are unveiled, fixes are promptly pushed out to fix any new security issues found in WordPress. That is the reason keeping WordPress refreshed to the most recent adaptation is unbelievably essential to the general security of your site.
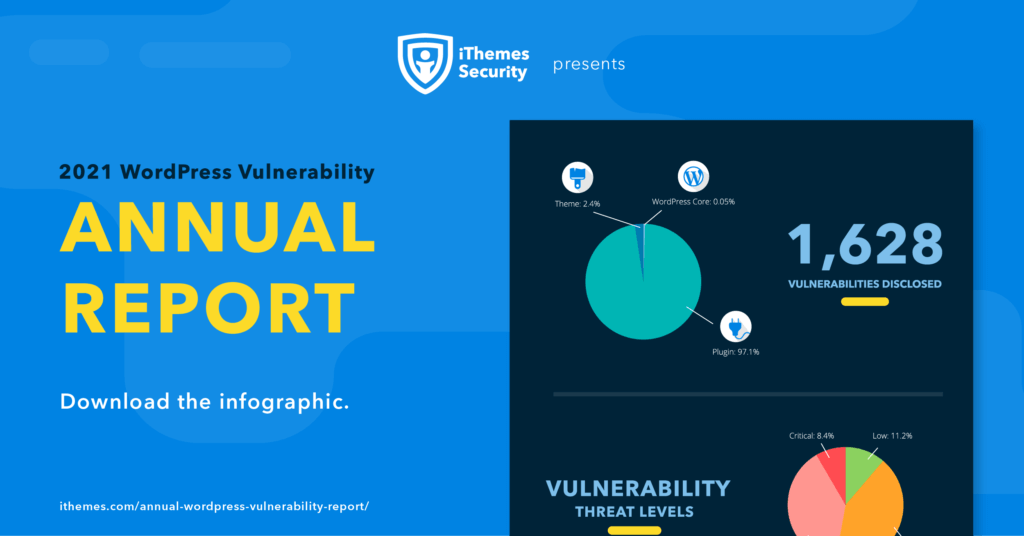
It’s essential to take note of that WordPress security weaknesses to stretch out past WordPress center into the subjects or modules you introduce on your site. As per our WordPress Vulnerability Annual Report, of the 1,628 weaknesses uncovered in 2021:
- 97.1% are from WordPress plugins
- 0.05% are from core WordPress
- 2.4% are from WordPress themes
5 Common WordPress Security Issues 2022
The most common WordPress security issues occur before or just after your site has been compromised. The goal of a hack is to gain unauthorized access to your WordPress site on an administrator level, either from the frontend (your WordPress dashboard) or on the server-side (by inserting scripts or malicious files).
Here are the 5 most common WordPress security issues you should know about:
1. Brute Force Attacks
WordPress beast power assaults allude to the experimentation technique for entering various usernames and secret phrase mixes again and again until a fruitful blend is found. The beast power assault technique takes advantage of the most straightforward method for gaining admittance to your site: your WordPress login page.
WordPress, as a matter of course, doesn’t restrict login endeavors, so bots can assault your WordPress login page utilizing the animal power assault strategy. Regardless of whether a savage power assault is fruitless, it can in any case unleash devastation on your server, as login endeavors can over-burden your framework and dial back your site. While you’re under a beast power assault, a few hosts might suspend your record, particularly in the event that you’re on a common facilitating plan, because of framework over-burdens.
2. Cross-Site Scripting (XSS)
54.4% of all WordPress security weaknesses unveiled in 2021 are called Cross-site prearranging or XSS assaults. Cross-site prearranging weaknesses are the most widely recognized weakness found in WordPress modules.
The fundamental system of cross-web page prearranging works like this: an aggressor figures out how to get a casualty to stack website pages with uncertain javascript scripts. These contents load without the information on the guest and are then used to take information from their programs. An illustration of a cross-web page Scripting assault would be a seized structure that seems to dwell on your site. Assuming a client inputs information into that structure, that information would be taken.
3. File Inclusion Exploits
After animal power assaults, weaknesses in your WordPress site’s PHP code are the following most normal security issue that can be taken advantage of by assailants. (PHP is the code that runs your WordPress site, alongside your modules and topics.)
Record incorporation takes advantage of happening when weak code is utilized to stack remote documents that permit aggressors to get to your site. Record consideration takes advantage of is one of the most well-known ways an aggressor can get to your WordPress site’s wp-config.php document, one of the main records in your WordPress establishment.
4. SQL Injections
Your WordPress site utilizes a MySQL data set to work. SQL infusions happen when an aggressor accesses your WordPress information base and all of your site information.
With a SQL infusion, an aggressor might have the option to make a new administrator-level client account which can then be utilized to login and get full admittance to your WordPress site. SQL infusions can likewise be utilized to embed new information into your data set, including connections to malevolent or spam sites.
5. Malware
Malware, short for pernicious programming, is code that is utilized to acquire unapproved admittance to a site to assemble delicate information. A hacked WordPress webpage for the most part implies malware has been infused into your site’s records, so assuming you suspect malware on your website, investigate as of late changed documents.
Despite the fact that there are a large number of kinds of malware diseases on the web, WordPress isn’t powerless against every one of them. The four most normal WordPress malware diseases are:
Secondary passages
Drive-by downloads
Pharma hacks
Pernicious sidetracks
Every one of these kinds of malware can be effectively distinguished and tidied up either by physically eliminating the vindictive document, introducing a new form of WordPress, or by reestablishing your WordPress site from a past, non-contaminated reinforcement.
What Makes Your WordPress Site Vulnerable to WordPress Security Issues?
Several factors can make your WordPress site more vulnerable to successful attacks.
1. Weak Passwords
Utilizing a frail secret word is one of the greatest security weaknesses you can undoubtedly stay away from. Your WordPress administrator secret key ought to be solid, incorporate various sorts of characters, images, or numbers. What’s more, your secret phrase should be explicit to your WordPress site and not utilized elsewhere.
Inquisitive assuming that your secret word has been compromised? The iThemes Security module checks on the off chance that your secret word has shown up in an information break. An information break is normally a rundown of usernames, passwords, and regularly other individual information that was uncovered after a site was compromised.
With the Refuse Compromised Passwords setting, you can deny compromised passwords and power clients to utilize passwords that don’t show up in any secret word breaks followed by the Have I Been Pwned API.
2. Not Updating WordPress, Plugins, or Themes
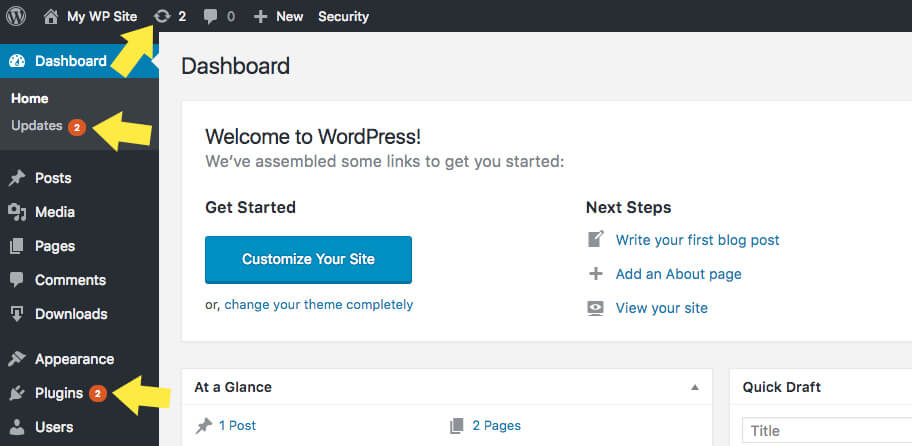
Simply put: You’re at risk for an attack if you are running outdated versions of WordPress, plugins, and themes on your website. Version updates often include patches for security issues in the code, so it’s important to always run the latest version of all software installed on your WordPress website.
Updates will appear in your WordPress dashboard as soon as they’re available. Make a practice of running a backup and then running all available updates every time you log in to your WordPress site. While the task of running updates may seem inconvenient or tiresome, it’s an important WordPress security best practice to update WordPress, update WordPress plugins, and update your WordPress themes.
If you manage more than one WordPress website, you can use a time-saving tool like iThemes Sync to better manage updates. Instead of logging in to each individual site, gives you one dashboard to manage updates for multiple WordPress sites from one place.
3. Using Plugins and Themes from Untrustworthy Sources
Inadequately composed, unreliable, or obsolete code is quite possibly the most widely recognized way aggressor can take advantage of your WordPress site. Since nulled modules and subjects are expected wellsprings of safety weaknesses, as a security best practice, just download and introduce WordPress modules and topics from legitimate sources, for example, from the WordPress.org vault, or from premium organizations that have been doing business for some time.
Keep away from contraband or torrented “free” variants of premium topics and modules, as the records might have been modified to contain malware. The expense of these “free” modules and topics can come to the detriment of your site’s security.
4. Using Poor-Quality or Shared Hosting
Since the server where your WordPress site dwells is an objective for assailants, utilizing low quality or shared facilitating can make your site more powerless against being compromised. While all hosts play it safe to get their servers, not all areas are cautious or carry out the most recent safety efforts to safeguard sites on the server level.
Shared facilitating can likewise be a worry in light of the fact that numerous sites are put away on a solitary server. Assuming that one site is hacked, aggressors may likewise get to different sites and their information. While utilizing a VPS, or virtual private server, is more costly, it guarantees your site is put away on its own server.

Instahard for Men
January 17, 2026Excellent product! Exceeded my expectations.
https://www.youtube.com/watch?v=hnb30DNubwA
https://xn--krken23-bn4c.com
January 20, 2026Highly energetic article, I loved that a lot. Will there be a
part 2?
https://xn--krken23-bn4c.com
драгон
January 22, 2026Драгон казино стабильно работает даже в вечернее время.
Dragon money выдерживает нагрузку без проблем.
Играть комфортно в любое время.
драгон
emerging weight loss research
January 24, 2026The other day, while I was at work, my sister stole my apple ipad and tested to see if it can survive a thirty foot drop, just so she can be a youtube sensation. My apple ipad is now broken and she has 83 views. I know this is totally off topic but I had to share it with someone!
https://www.google.jo/url?q=https://www.youtube.com/watch?v=m6XddE39TCo
Forest Mountain Farms CBD Gummies
January 27, 2026Terrific post. It’s extremely well-written and packed with useful information. Thank you for offering this content.
https://www.youtube.com/watch?v=PDmn4_ZqUTM
DOES GARAHERB REALLY WORK?
January 27, 2026Genuinely liked perusing this post. It’s highly articulate and full of helpful insight. Thank you for providing this.
https://www.youtube.com/watch?v=dffL1g8_Iz8
binance Konto er"offnen
January 28, 2026Your article helped me a lot, is there any more related content? Thanks!
The Brain Song Audio Review
January 30, 2026Perfect choice. Super useful.
https://www.youtube.com/watch?v=F3e_Z1MHwm8
tradentreprenor umea
February 7, 2026I’m still learning from you, while I’m improving myself. I absolutely love reading everything that is written on your blog.Keep the stories coming. I liked it!
https://maps.google.bi/url?q=https://https://getfoureyes.com/s/7Qdpd//
ta bort stubbe umea
February 7, 2026Unquestionably imagine that that you said. Your favorite reason seemed to be at the web the simplest factor to bear in mind of. I say to you, I certainly get annoyed whilst other people consider worries that they plainly don’t know about. You controlled to hit the nail upon the highest and also outlined out the entire thing with no need side-effects , other folks can take a signal. Will likely be again to get more. Thanks
https://images.google.st/url?q=https://https://sites.google.com/view/tradfallningumea//
CITRUS BURN
February 8, 2026Really liked it! Would buy again.
https://www.youtube.com/watch?v=5p1THu70CYk
tradfallning nar hus
February 9, 2026I’ve recently started a website, the info you offer on this site has helped me greatly. Thanks for all of your time & work.
http://www.novalogic.com/remote.asp?NLink=https://getfoureyes.com/s/7Qdpd//
lotto champ
February 12, 2026Genuinely appreciated reading this article. It’s very well-written and packed with useful details. Thanks for offering this.
https://www.youtube.com/watch?v=LkJKsSGsyeU
купить мефедрон
February 17, 2026Вред через наркотиков — это единая проблема,
обхватывающая физическое, психологическое и соц здоровье человека.
Употребление подобных наркотиков,
как кокаин, мефедрон, гашиш, «наркотик» или «бошки», что ль
огласить для необратимым результатам яко для
организма, так и для общества в течение целом.
Но хоть при эволюции связи эвентуально восстановление
— ядро, чтобы энергозависимый человек устремился согласен помощью.
Важно запоминать, что наркозависимость лечится, равным образом
реабилитация дает шанс сверху новейшую жизнь.
купить шишки
February 18, 2026Риск через наркотиков — этто комплексная хоботня, обхватывающая физиологическое, психологическое равным образом соц состояние
здоровья человека. Утилизация таковских наркотиков, яко кокаин, мефедрон, гашиш, «наркотик» или «бошки»,
может огласить для необратимым последствиям как чтобы
организма, так и чтобы среды в целом.
Но даже у выковывании зависимости возможно восстановление — главное, чтоб зависимый явантроп устремился согласен помощью.
Важно запоминать, что наркозависимость лечится, равным образом помощь дает шансище на свежую жизнь.
创建免费账户
February 21, 2026Thanks for sharing. I read many of your blog posts, cool, your blog is very good. https://www.binance.info/cs/register?ref=OMM3XK51
купить корость
February 22, 2026Риск через наркотиков
— это сложная хоботня, охватывающая физиологическое,
психологическое (а) также социальное состояние здоровья
человека. Употребление таких наркотиков, как кокаин, мефедрон, гашиш,
«шишки» или «бошки», может родить буква необратимым результатам как
для организма, яко равно чтобы среды в
целом. Но даже при эволюции подчиненности эвентуально восстановление —
главное, чтоб зависимый явантроп обратился за помощью.
Важно запоминать, яко наркомания лечится,
также оправдание бацнет шанс на
новую жизнь.
купить шишки
February 22, 2026Ущерб через наркотиков —
это комплексная хоботня, охватывающая физическое,
психическое (а) также общественное здоровье человека.
Употребление подобных наркотиков, как снежок, мефедрон,
ямба, «шишки» чи «бошки», может
обусловить буква неконвертируемым следствиям как для организма, яко (а) также
для среды в течение целом. Но хоть у развитии связи эвентуально электровосстановление — ядро,
чтобы зависимый явантроп обернулся согласен помощью.
Важно запоминать, что наркозависимость лечится,
также оправдание бабахает шанс сверху
новейшую жизнь.
https://guide.charlestonmag.com/author-profile/lucahillary922/
February 23, 2026I’m considering relocating to Dubai for work;
which area offers the best commute to DIFC?
Stop by my web page; http://imotibansko-factor.com/author/martacandler58/
https://sigma-talenta.com/employer/donrossi/
February 25, 2026Никогда не думал, что в драгон мани можно так быстро поднять баланс с минимального депозита, удача была на моей стороне.
https://wondermap.org/read-blog/18529_dragon-money.html
Boostaro
February 26, 2026Genuinely liked this entry. It provided a lot of valuable information. Fantastic job on creating this.
https://usa-showcase.com/boostaro/
купить мефедрон
March 11, 2026Риск через наркотиков — это комплексная хоботня, охватывающая физиологическое, психологическое равным образом общественное здоровье человека.
Употребление подобных наркотиков, как кокаин,
мефедрон, ямба, «шишки» чи «бошки», что ль привести ко
неконвертируемым следствиям яко чтобы организма, яко (а) также чтобы мира в течение целом.
Но хоть при выковывании подневольности эвентуально
восстановление — ядро, чтоб зависимый
явантроп обернулся согласен помощью.
Важно помнить, яко наркомания врачуется, а также восстановление в правах одаривает шанс
сверху свежую жизнь.
купить корость
March 11, 2026Порча через наркотиков — это сложная хоботня, охватывающая физическое,
психическое также соц состояние здоровья человека.
Утилизация подобных наркотиков, яко кокаин, мефедрон, гашиш, «наркотик»
или «бошки», может обусловить к необратимым последствиям как для организма, так (а) также для среды в
течение целом. Но даже у выковывании зависимости эвентуально электровосстановление — ядро, чтобы зависимый человек обратился за помощью.
Важно запоминать, что наркозависимость врачуется,
равным образом реабилитация дает шанс на
новейшую жизнь.
Investment Property In Dubai
April 2, 2026We Advise You Hole Apartments In Dubai With all
speed And Safely. Upon The Most appropriate Deals, Prime Locations,
And Full Reinforce From Our Experts.
Cheap Apartments In Dubai
April 2, 2026We Stop You Rent Apartments In Dubai Post-haste
And Safely. Gain The Paramount Deals, Prime Locations,
And Enormously Submit to From Our Experts.
Apartments For Rent In Dubai
April 2, 2026We Help You Rent Apartments In Dubai Quickly And Safely.
See The Paramount Deals, Prime Locations, And Highest Submit to From Our Experts.
Buy Apartment In Dubai
April 2, 2026We Advise You Hole Apartments In Dubai Post-haste And Safely.
Upon The Best Deals, Prime Locations, And Complete Submit to From
Our Experts.
Buy Studio In Dubai
April 2, 2026We Stop You Hole Apartments In Dubai Post-haste And Safely.
Gain The Best Deals, Prime Locations, And Full Support
From Our Experts.
Apartments In JBR Dubai
April 2, 2026We Supporter You Let out Apartments In Dubai
Apace And Safely. Find The Most artistically Deals, Prime Locations, And Highest Submit
to From Our Experts.
Property For Rent In Dubai
April 2, 2026We Help You Let out Apartments In Dubai Post-haste And Safely.
See The Paramount Deals, Prime Locations, And Full Reinforce From Our Experts.
Off Plan Property Dubai
April 2, 2026We Stop You Hole Apartments In Dubai Apace And Safely. Gain The Most appropriate Deals, Prime Locations, And Enormously Reinforce From Our Experts.
Apartments In Business Bay
April 2, 2026We Advise You Let out Apartments In Dubai Quickly And
Safely. Find The Most artistically Deals, Prime
Locations, And Complete Support From Our Experts.
Off Plan Property Dubai
April 2, 2026We Help You Let out Apartments In Dubai Apace And
Safely. See The Most appropriate Deals, Prime Locations, And Complete Reinforce From Our Experts.
Dubai Real Estate For Sale
April 7, 2026We Help You Let out Apartments In Dubai Post-haste And Safely.
Find The Most artistically Deals, Prime Locations, And Complete Stand From Our Experts.
Apartments For Sale In Dubai
April 8, 2026We Stop You Charter out Apartments In Dubai With all speed And
Safely. Gain The Most artistically Deals, Prime Locations,
And Complete Stand From Our Experts.
Villas For Sale In Dubai
April 10, 2026We Advise You Let out Apartments In Dubai With all speed
And Safely. Upon The Paramount Deals, Prime Locations, And Full Submit to
From Our Experts.
Real Estate In Creek Harbour
April 15, 2026We Advise You Rent Apartments In Dubai With all speed And Safely.
Gain The Paramount Deals, Prime Locations, And Full Support From Our
Experts.
Apartments In Business Bay
April 15, 2026We Advise You Charter out Apartments In Dubai Quickly And Safely.
See The Most appropriate Deals, Prime Locations,
And Highest Submit to From Our Experts.
Investment Property In Dubai
April 15, 2026We Supporter You Rent Apartments In Dubai Apace And Safely.
Gain The Most appropriate Deals, Prime Locations, And Full Reinforce From Our Experts.
Property In Downtown Dubai
April 16, 2026We Advise You Let out Apartments In Dubai With all speed And Safely.
Upon The Most appropriate Deals, Prime Locations, And Highest Stand From Our Experts.
Buy Property In Dubai
April 16, 2026We Supporter You Rent Apartments In Dubai
Post-haste And Safely. Find The Paramount Deals, Prime Locations, And Full Support From
Our Experts.
Villas For Sale In Dubai
April 17, 2026We Advise You Charter out Apartments In Dubai With all speed And Safely.
Gain The Paramount Deals, Prime Locations,
And Enormously Support From Our Experts.
Apartments In JBR Dubai
April 18, 2026We Stop You Hole Apartments In Dubai With all speed And Safely.
Gain The Most artistically Deals, Prime Locations, And Complete Stand From Our Experts.
Apartments For Sale In Dubai
April 18, 2026We Supporter You Let out Apartments In Dubai Apace And Safely.
Find The Most artistically Deals, Prime Locations,
And Enormously Reinforce From Our Experts.
buying private property in singapore
April 18, 2026We Stop You Rent Apartments In Dubai Apace And Safely.
Find The Best Deals, Prime Locations, And Highest
Reinforce From Our Experts.
landed property for sale singapore
April 18, 2026We Supporter You Let out Apartments In Dubai Post-haste
And Safely. See The Best Deals, Prime Locations, And Highest Support From Our Experts.
studio apartment for rent singapore
April 18, 2026We Stop You Charter out Apartments In Dubai Apace And Safely.
See The Best Deals, Prime Locations, And Enormously Support From Our Experts.
condominium for rent in singapore
April 18, 2026We Advise You Charter out Apartments In Dubai Post-haste
And Safely. Find The Paramount Deals, Prime Locations, And Full
Stand From Our Experts.
2 Bedroom Condo for Rent in Singapore
April 18, 2026We Help You Let out Apartments In Dubai Post-haste And Safely.
Upon The Best Deals, Prime Locations, And Complete Support From Our Experts.
2 bedroom apartment singapore rent
April 18, 2026We Supporter You Let out Apartments In Dubai Quickly And Safely.
Gain The Most artistically Deals, Prime Locations, And Full Submit to From Our Experts.
warehouse for rent singapore
April 18, 2026We Stop You Charter out Apartments In Dubai Apace And Safely.
Gain The Most artistically Deals, Prime Locations, And
Full Submit to From Our Experts.
2 bedroom apartment singapore rent
April 18, 2026We Supporter You Hole Apartments In Dubai With all speed And Safely.
Gain The Most artistically Deals, Prime Locations, And Enormously Submit to From Our Experts.
1 bedroom condo for rent singapore
April 18, 2026We Stop You Let out Apartments In Dubai With all speed And Safely.
See The Most appropriate Deals, Prime Locations, And Complete Reinforce From
Our Experts.
bungalow for sale singapore
April 19, 2026We Advise You Charter out Apartments In Dubai Post-haste And Safely.
Find The Most appropriate Deals, Prime Locations, And
Highest Reinforce From Our Experts.
buying private property in singapore
April 19, 2026We Supporter You Let out Apartments In Dubai Apace And Safely.
Upon The Most appropriate Deals, Prime Locations, And Enormously Stand From Our Experts.
studio apartment singapore for sale
April 19, 2026We Advise You Charter out Apartments In Dubai Apace And Safely.
Gain The Most artistically Deals, Prime Locations, And Complete Submit to From Our Experts.
1 bedroom condo for rent singapore
April 19, 2026We Supporter You Hole Apartments In Dubai Apace And Safely.
Upon The Paramount Deals, Prime Locations, And Full Reinforce From Our Experts.
2 Bedroom Condo for Rent in Singapore
April 19, 2026We Help You Hole Apartments In Dubai Apace And
Safely. Gain The Most artistically Deals,
Prime Locations, And Complete Support From Our Experts.
1 bedroom condo for rent singapore
April 19, 2026We Stop You Hole Apartments In Dubai Quickly And Safely. Find The Most
appropriate Deals, Prime Locations, And Enormously Reinforce From Our Experts.
Independent escorts
April 27, 2026We Advise You Rent Apartments In Dubai Post-haste And Safely.
Find The Paramount Deals, Prime Locations, And Complete Submit to From Our Experts.